What’s New with Convene?
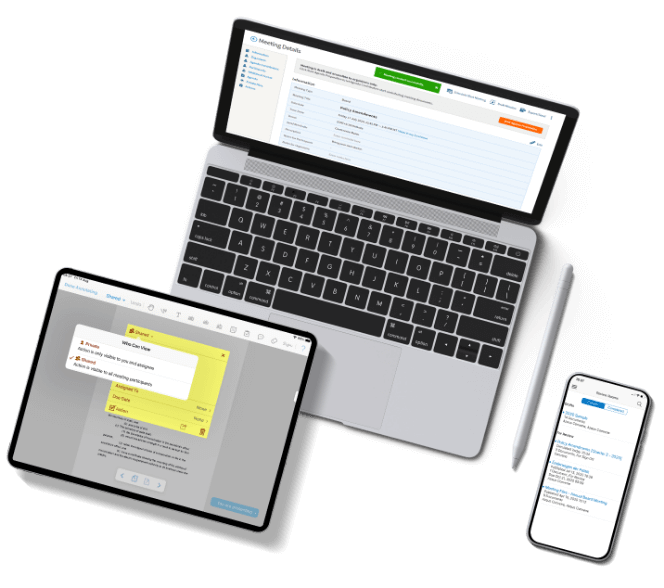
View documents and join meetings without installing the App. Convene Web is made for directors, allowing you to access Convene via any web browser.
For Directors and Executives
With Convene, directors and executives can easily collaborate in real-time and make informed decisions anytime, anywhere.



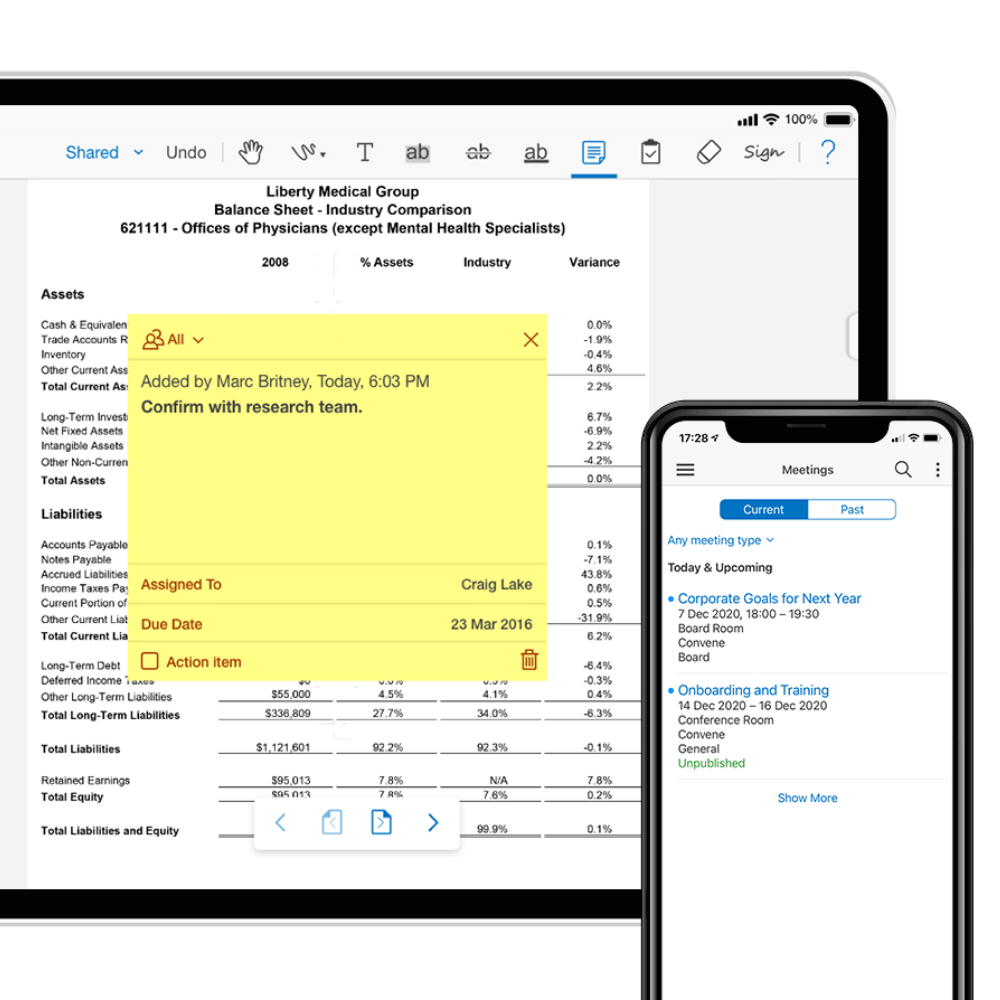
Pre-Meeting
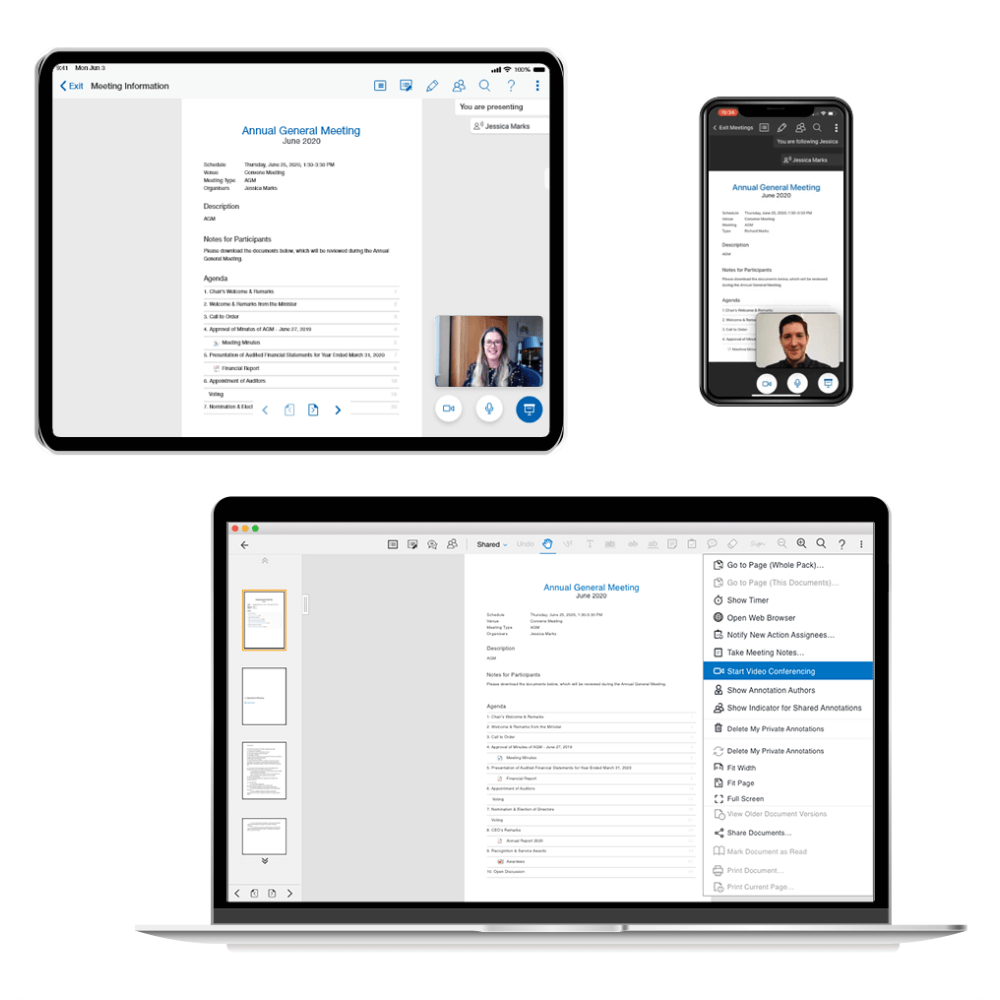
During Meeting
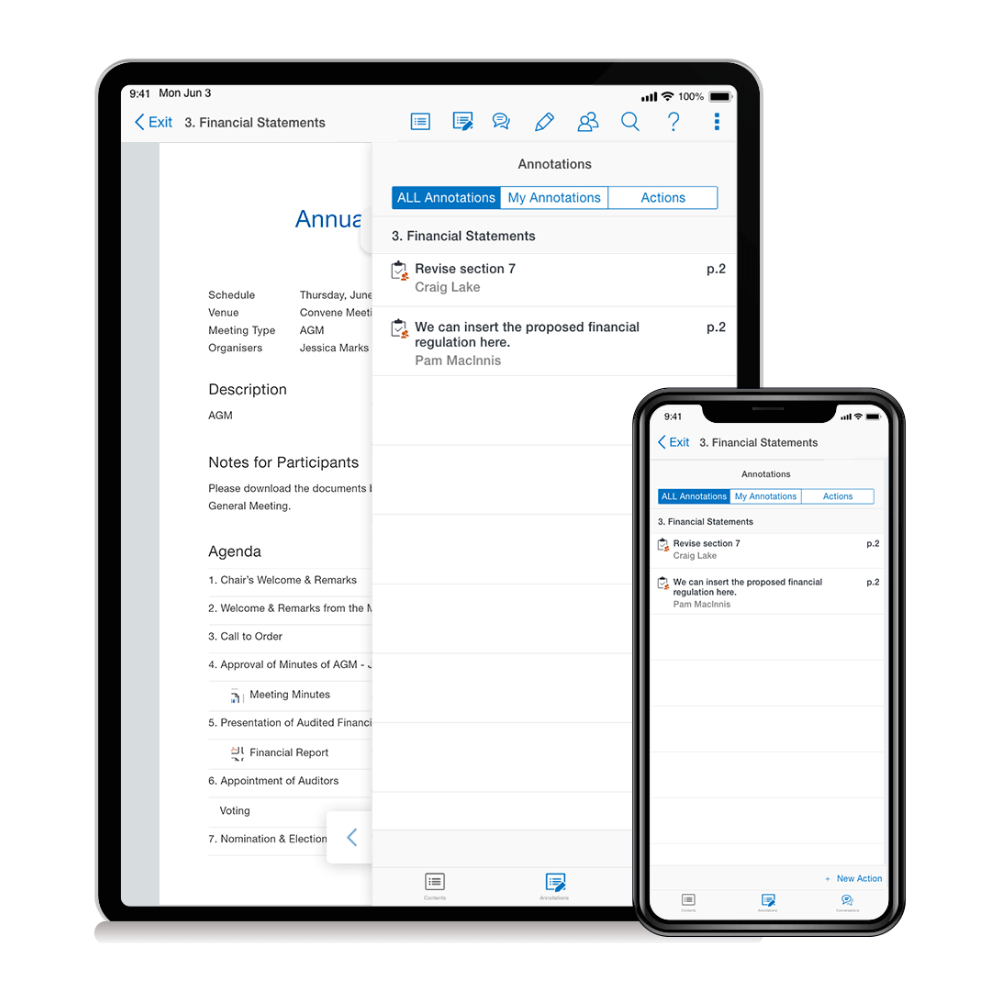
Post-Meeting
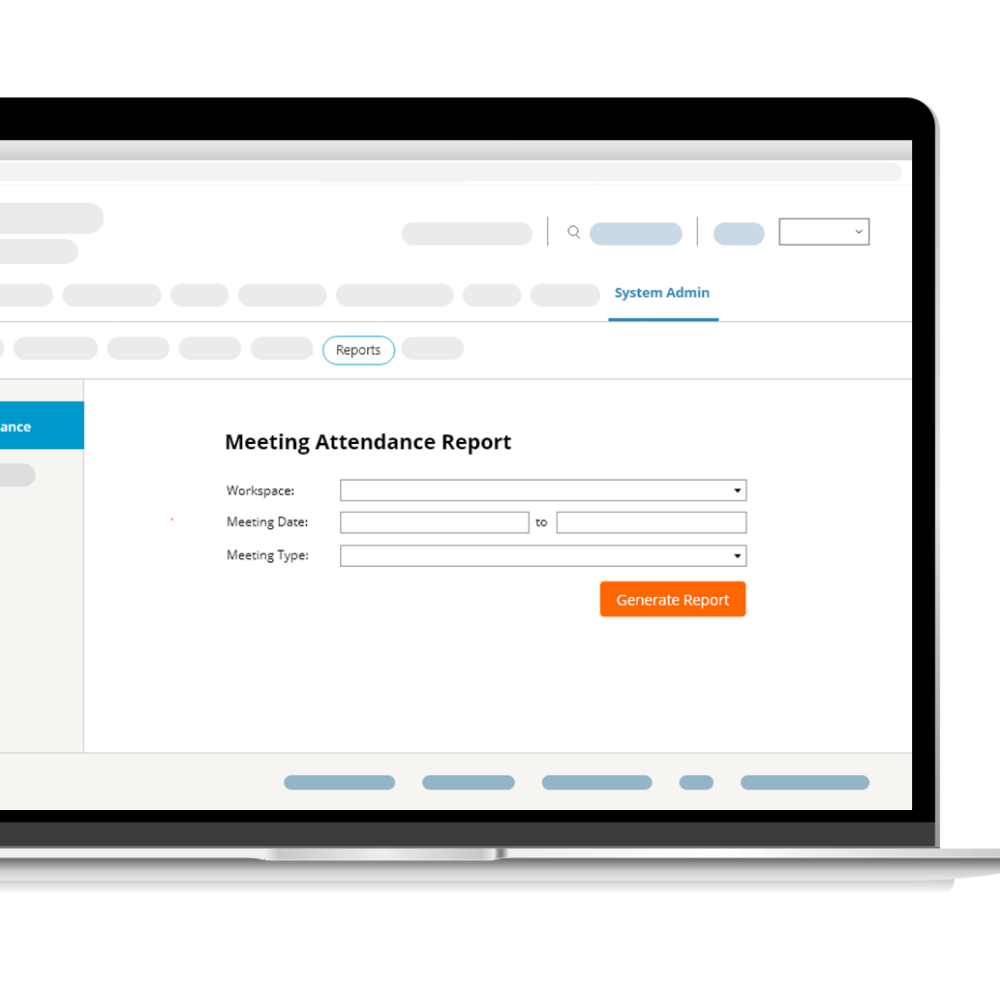
For Administrators and Secretaries
Convene reduces the time and effort spent by administrators and secretaries in preparing for meetings, allocating resources to more value-adding projects instead.



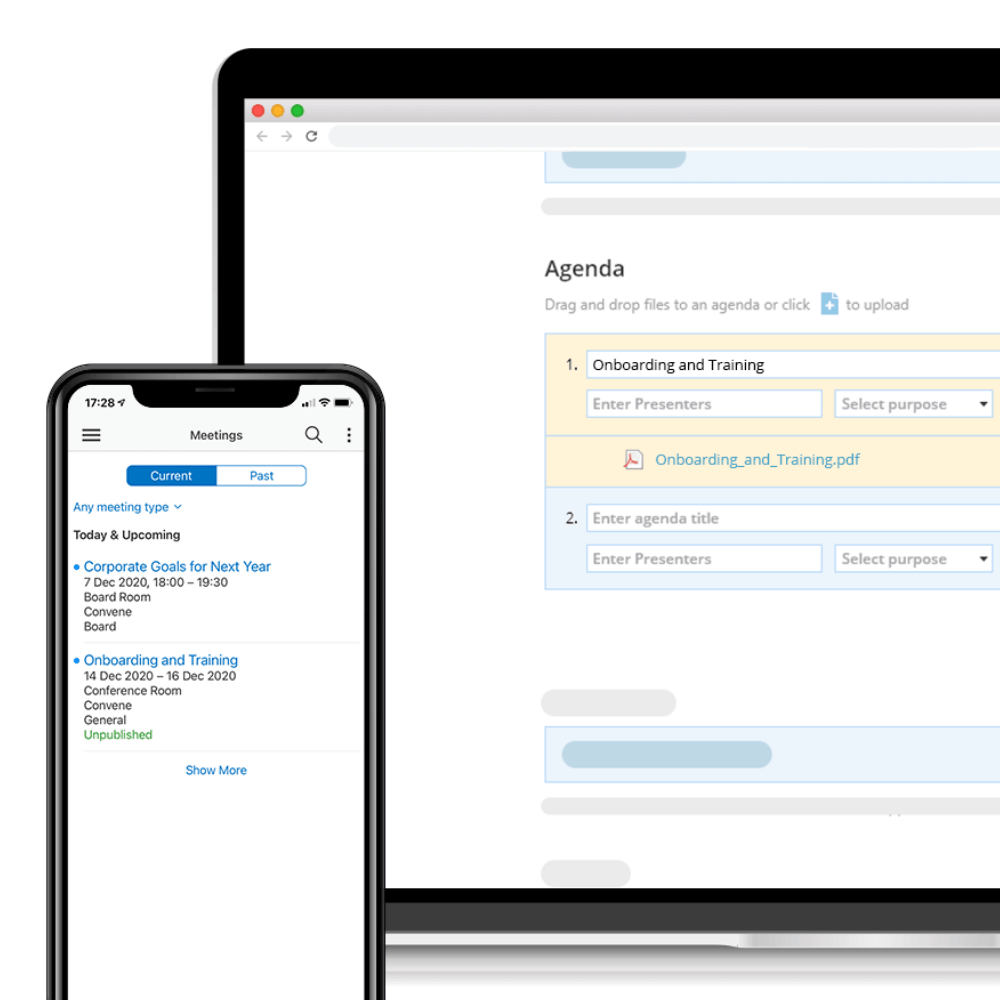
Pre-Meeting
During Meeting
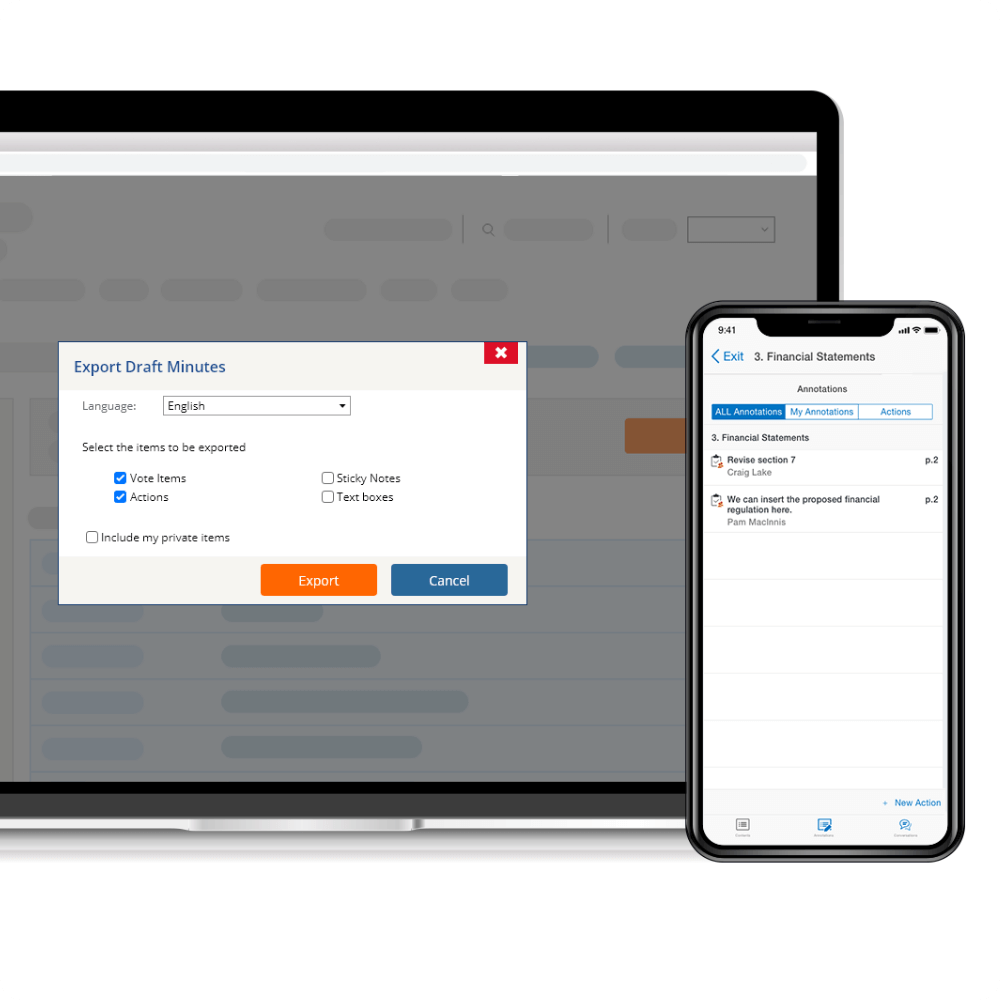
Post-Meeting
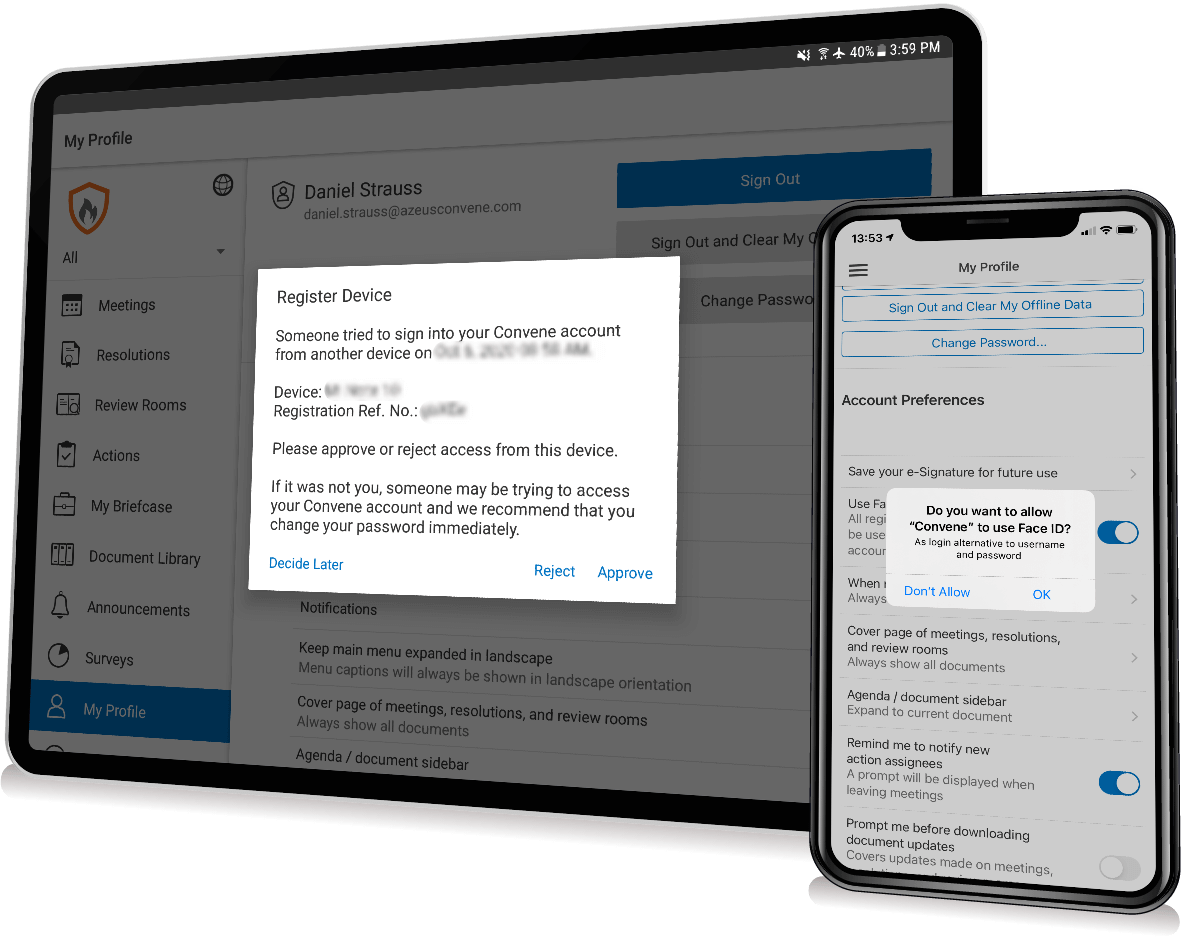
Security at a Glance
As a premier board management software, we implement the highest security standards for your organization.
Make all your meetings smart, simple, and secure
Learn how Convene can give your boards a superior meeting experience. Enquire for a free demo with no cost or obligation.